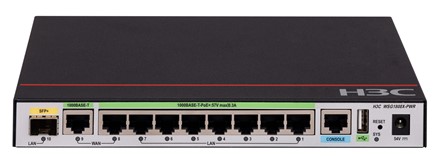
H3C WSG1808X-PWR Wireless Integrated Multi-Service Router Gateway
รหัสสินค้า : H3C WSG1808X-PWR
| ราคา |
14,900.00 บาท |
| จำนวนที่จะซื้อ | |
| ราคารวม | 14,900.00 บาท |
สินค้าไม่เพียงพอ
สินค้าหมด
H3C WSG1808X-PWR 10-Port (9*1000BASE-T and 1*SFP Plus) Integrated Multi-Service Router Gateway
Model: H3C WSG1812X-PWR
H3C WSG1812X-PWR Datasheet Download
H3C WSG1808X-PWR Wireless Integrated Services Gateway Installation Guide
ทางร้านเป็นตัวแทนแต่งตั้ง จากทาง H3C Authorized Thailand
มีราคาพิเศษ งานโครงการ ช่าง ร้านค้า ผู้รับเหมา และออกเอกสารงานโครงการ
พร้อมบริการ แนะนำติดตั้ง ใช้งาน เซ็ต ตั้งค่า ทดสอบเบื้องต้นให้
ติดต่อสอบถามทักไลน์ 0897993376
Hardware Specifications
WAN Port :2*GE
LAN Port:7*GE PoE plus+ 1*SFP+
Notes : All ports are LAN/WAN switchable. WAN ports are the 8th and the 9th port; the 10th port is SFP+ port
1*Console
Wireless throughput : 2Gbps
Power supplies : Power adapter
Software specifications
Item
Feature
WSG1808X-PWR
Basic functions
Number of managed APs by default
12 ordinary APs or 24 wall-plate APs
Maximum number of managed APs
24
(Notes: 1 license per ordinary AP, 0.5 license per wall-plate AP, but 24 APs at most)
Maximum users of authentication
1024
802.11MAC
802.11 Protocols
√
The number of SSID of whole machine
24
SSID hiding
√
11G protection
√
11n only
√
Use number limit
Supported: SSID based, per RF based
Keepalive
√
Idle
√
Multi-country code assignment
√
Wireless user isolation
Supported:
VLAN based wireless users 2-layer isolation
SSID based wireless user 2-layer isolation
20MHz/40MHz auto-switch in 40MHz mode
√
Local forwarding
Local forwarding based on SSID+VLAN
CAPWAP
Automatic AP registration
√
AC discovery (DHCP option43, DNS)
√
IPv6 tunnel
√
Clock synchronization
√
Jumbo frame forwarding
√
Assign basic AP network parameter through AC
Supported: Static IP, VLAN, connected AC address
L2/L3 connection between AP and AC
√
NAT traversal between AP and AC
√
Roaming
Intra-AC, Inter-AP L2 and L3 roaming
√
Inter-AC, Inter-AP L2 and L3 roaming
√
GW Features
NAT
√
PPPoE
√
DDNS
√
SSL VPN
√
IPSEC VPN
√
RIP
√
GRE
√
Access control
Open system, Shared-Key
√
WEP-64/128, dynamic WEP
√
WPA, WPA2, WPA3
√
TKIP
√
CCMP
√(11n recommended)
SSH v1.5/v2.0
√
Portal authentication
Supported: Remote Authentication, external server
Portal page redirection
Supported: SSID based, AP Portal page push
Portal by-pass Proxy
√
802.1x authentication
EAP-TLS, EAP-TTLS, EAP-PEAP, EAP-MD5, EAP-SIM, LEAP, EAP-FAST, EAP offload (TLS, PEAP only)
Local authentication
802.1X, Portal, MAC authentication
LDAP authentication
802.1X and Portal
EAP-GTC and EAP-TLS supported by 802.1X login
AP location-based user access control
√
Guest Access control
√
VIP channel
√
ARP attack detection
Supported: Wireless SAVI
SSID anti-spoofing
SSID + user name binding
AAA server selection based on SSID and domain
√
AAA server back up
√
Local AAA server for wireless user
√
TACACS+
√
QoS
Priority mapping
√
L2-L4 packet filtering and traffic classification
√
Rate limit
Supported with granularity of 8Kbps
802.11e/WMM
√
Access control based on user profile
√
Intelligent bandwidth limit (equal bandwidth share algorithm)
√
Intelligent bandwidth limit (user specific)
√
Intelligent bandwidth guarantee
Supported: Free flow for packets coming from every SSID When traffic is not congested, and guarantee a minimum bandwidth for each SSID when traffic is congested
QoS Optimization for SVP phone
√
CAC (Call Admission Control)
Supported: based on user number/bandwidth
End-to-end QoS
√
AP upload speed limit
√
RF management
Country code lock
√
Static channel and power configuration
√
Auto channel and power configuration
√
Auto transmission rate adjustment
√
Coverage hole detection and correction
√
Load balancing
Supported: based on traffic, user & frequency (dual-frequency supported)
Intelligent load balancing
√
AP load balancing group
Supported: auto-discovery and flexible setting
Security
Static blacklist
√
Dynamic blacklist
√
White list
√
Rogue AP detection
Supported: SSID based, BSSID, device OUI
Rouge AP countermeasure
√
Flooding attack detection
√
Spoof attack detection
√
Weak IV attack detection
√
WIPS/WIDS
Supported: 7-layer mobile security
Layer 2 protocol
ARP (gratuitous ARP)
√
802.1p
√
802.1q
√ (Maximum VLANs: 4094)
802.1x
√
IP protocol
IPv4 protocol
√
Native IPv6
√
IPv6 SAVI
√
IPv6 Portal
√
Multicast
MLD Snooping
√
IGMP Snooping
√
Multicast group
256
Multicast to Unicast (IPv4, IPv6)
Supported: Set unicast limit based on operating environment
Redundancy
1+1 failover between ACs
√
Intelligent AP sharing among ACs
√
Remote AP
√
Management and deployment
Network management
WEB, SNMP v1/v2/v3, RMON
Network deployment
WEB, CLI, Telnet, FTP
Green features
Scheduled shutdown of AP RF interface
√
Scheduled shutdown of wireless service
√
Per-packet power adjustment (PPC)
√
WLAN
Application
RF Ping
√
Remote probe analysis
√
Packet forwarding fairness adjustment
√
802.11n packet forwarding suppression
√
Access based traffic shaping
√
Co-AP channel sharing
√
Co-AP channel reuse
√
RF interface transmission rate adjustment algorithm
√
Drop wireless packet with weak signal
√
Disable user access with weak signal
√
Disable multicast packet caching
√
Status blink (limited to some AP)
√
New added features
Policy forwarding
√
VLAN pool
√
Bonjour gateway
√
802.11w
√
802.11k, v, r
√
Hotspot2.0 (802.11u)
√
NAT
√
VPN
√
Firewall
Attack protection against malicious attacks, such as land, smurf, fraggle, ping of death, teardrop, IP spoofing, IP fragmentation, ARP spoofing, reverse ARP lookup, invalid TCP flag, large ICMP packet, address/port scanning, SYN flood, ICMP flood, UDP flood, and DNS query flood
√
ASPF application layer packet filtering
√
Basic and advanced ACLs
√
Time range-based ACL
√
User-based and application-based access control
√
Static and dynamic blacklist function
√
MAC-IP binding
√
MAC-based ACL
√
Antivirus
Signature-based virus detection
√
Manual and automatic upgrade for the signature database
√
Stream-based processing
√
Virus detection based on HTTP, FTP, SMTP, and POP3
√
Virus types include Backdoor, Email-Worm, IM-Worm, P2P-Worm, Trojan, AdWare, and Virus
√
Virus logs and reports
√
Signature-based virus detection
√
Deep intrusion prevention
Prevention against common attacks such as hacker, worm/virus, Trojan, malicious code, spyware/adware, DoS/DDoS, buffer overflow, SQL injection, and IDS/IPS bypass
√
Attack signature categories (based on attack types and target systems) and severity levels (including high, medium, low, and notification)
√
Manual and automatic upgrade for the attack signature database (TFTP and HTTP).
√
P2P/IM traffic identification and control
√
Email/webpage/application layer filtering
Email filtering
√
SMTP email address filtering
√
Email subject/content/attachment filtering
√
Webpage filtering
√
HTTP URL/content filtering
√
VPN
L2TP VPN
√
IPSec VPN
√
GRE VPN
√
SSL VPN
√
NAT
Many-to-one NAT, which maps multiple internal addresses to one public address
√
Many-to-many NAT, which maps multiple internal addresses to multiple public addresses
√
One-to-one NAT, which maps one internal address to one public address
√
NAT of both source address and destination address
√
External hosts access to internal servers
√
Internal address to public interface address mapping
√
NAT support for DNS
√
Setting effective period for NAT
√
NAT ALGs for NAT ALG, including DNS, FTP, H.323, ILS, MSN, NBT, PPTP, and SIP
√